What is user authorization

Sophia Edwards
Published Apr 09, 2026
What Is Authorization? Authorization in system security is the process of giving the user permission to access a specific resource or function. This term is often used interchangeably with access control or client privilege.
What comes first authentication or authorization?
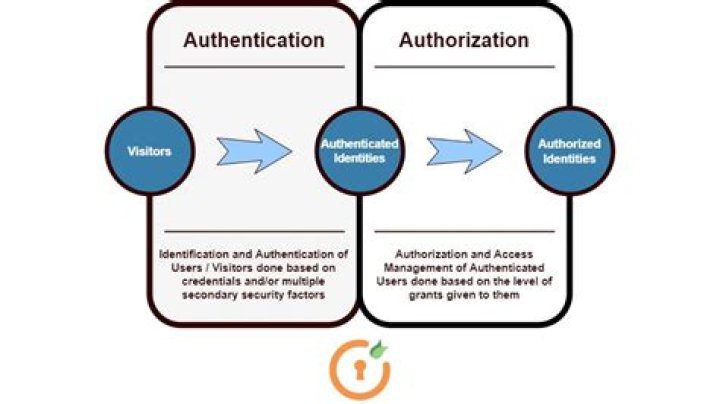
In authentication process, the identity of users are checked for providing the access to the system. … Authentication is done before the authorization process, whereas authorization process is done after the authentication process.
What is authorization example?
Authorization is the process of giving someone the ability to access a resource. … For instance, accessing the house is a permission, that is, an action that you can perform on a resource. Other permissions on the house may be furnishing it, cleaning it, repair it, etc.
What is authentication and authorization Why are these two used together?
Both the terms are often used in conjunction with each other when it comes to security and gaining access to the system. … Authentication means confirming your own identity, whereas authorization means being allowed access to the system.What is authentication in cyber security?
Definition: Authentication is the process of recognizing a user’s identity. … The credentials provided are compared to those on a file in a database of the authorized user’s information on a local operating system or within an authentication server.
What are the three types of authentication?
Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.
What is difference b/w authentication and authorization?
Simply put, authentication is the process of verifying who someone is, whereas authorization is the process of verifying what specific applications, files, and data a user has access to.
Why do we need user authentication?
User authentication is a method that keeps unauthorized users from accessing sensitive information. For example, User A only has access to relevant information and cannot see the sensitive information of User B. Cybercriminals can gain access to a system and steal information when user authentication is not secure.Is OAuth for authentication or authorization?
OAuth doesn’t share password data but instead uses authorization tokens to prove an identity between consumers and service providers. OAuth is an authentication protocol that allows you to approve one application interacting with another on your behalf without giving away your password.
What is the difference between user identification and user authentication?Identification is the ability to identify uniquely a user of a system or an application that is running in the system. Authentication is the ability to prove that a user or application is genuinely who that person or what that application claims to be. … The system uses the user ID to identify the user.
Article first time published onWhat is the difference between Auth0 and OAuth?
OAuth 2.0 is a protocol that allows a user to grant limited access to their resources on one site, to another site, without having to expose their credentials. Auth0 is an organisation, who manages Universal Identity Platform for web, mobile and IoT can handle any of them — B2C, B2B, B2E, or a combination.
How do I authenticate a user?
In authentication, the user or computer has to prove its identity to the server or client. Usually, authentication by a server entails the use of a user name and password. Other ways to authenticate can be through cards, retina scans, voice recognition, and fingerprints.
What is authentication and its types?
In computing, authentication is the process of verifying the identity of a person or device. A common example is entering a username and password when you log in to a website. … While a username/password combination is a common way to authenticate your identity, many other types of authentication exist.
What is the difference between authentication and authenticity?
Authentication is verification of identity (are you who you say you are). Examples include username/password and biometrics. Authenticity is verification of a message or document to ensure it wasn’t forged or tampered with.
What is authentication and authorization in security?
In simple terms, authentication is the process of verifying who a user is, while authorization is the process of verifying what they have access to. Comparing these processes to a real-world example, when you go through security in an airport, you show your ID to authenticate your identity.
What is authentication method?
Authentication is the method used to verify a user’s identity when the user is trying to access network resources. Windows Server 2003 offers several types of authentication protocols that allow users to use the single sign-on method to access the network.
What is Firewall OS?
A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. … A firewall can be hardware, software, or both.
What is authorization and authentication in API?
Authentication is stating that you are who are you are and Authorization is asking if you have access to a certain resource. When working with REST APIs you must remember to consider security from the start.
What are the types of authorization?
There are four types of Authorization – API keys, Basic Auth, HMAC, and OAuth.
What is authorization in API testing?
Involves checking resources that the user is authorized to access or modify via defined roles or claims. For example, the authenticated user is authorized for read access to a database but not allowed to modify it. The same can be applied to your API.
What is Kerberos Key?
Kerberos is a computer network security protocol that authenticates service requests between two or more trusted hosts across an untrusted network, like the internet. It uses secret-key cryptography and a trusted third party for authenticating client-server applications and verifying users’ identities.
What are the 5 factors of authentication?
- Knowledge Factors. Knowledge factors require the user to provide some data or information before they can access a secured system. …
- Possession Factors. …
- Inherence Factors. …
- Location Factors. …
- Behavior Factors.
What a user has?
A user often has a user account and is identified to the system by a username (or user name). Other terms for username include login name, screenname (or screen name), account name, nickname (or nick) and handle, which is derived from the identical citizens band radio term.
What is key clock?
Keycloak is an open source software product to allow single sign-on with Identity and Access Management aimed at modern applications and services.
Why is OAuth bad?
Let’s start with the biggest reason why OAuth isn’t authentication: access tokens are not intended for the client application. When an authorization server issues an access token, the intended audience is the protected resource. … It’s down to the protected resource to understand and validate the token.
What is difference between OAuth 1.0 and OAuth 2 O?
OAuth 2.0 signatures are not required for the actual API calls once the token has been generated. It has only one security token. OAuth 1.0 requires client to send two security tokens for each API call, and use both to generate the signature.
Why is authentication and authorization important?
Both authentication and authorization are required to deal with sensitive data assets. Without any of them, you are keeping data vulnerable to data breaches and unauthorized access. Protected resources require additional security steps like authentication and authorization.
What is IP authentication?
IP address authentication is the traditional method of identifying users requesting access to vendor databases. Users gain access based on their computer or site IP address (numerical address), eliminating the need for user IDs and passwords.
What happens if a company manages authentication and not authorization?
When dealing with access to any sort of sensitive data assets, both authentication and authorization are required. Without both, you risk exposing information via a breach or unauthorized access, ultimately resulting in bad press, customer loss and potential regulatory fines.
What is oauth crack your interview?
(1)Authentication with an “O”. (2)An open standard that allows users to share personal resources stored on a site with. another site, without having to share their credentials. (3)An open standard that allows users to securely share their credentials, typically. username and password with other websites or entities.
How does SSO work in mobile app?
Single sign-on (SSO) allows a user to sign in once and get access to other applications without re-entering credentials. This makes accessing apps easier and eliminates the need for users to remember long lists of usernames and passwords. Implementing it in your app makes accessing and using your app easier.