What is SQL injection Java

Robert Spencer
Published Apr 20, 2026
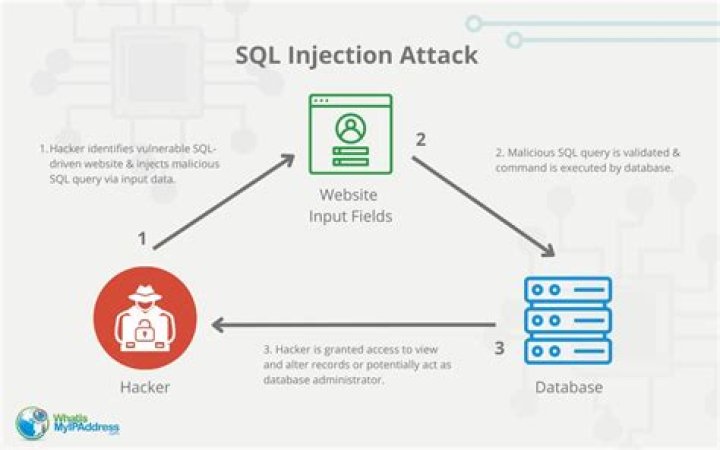
In simple words, SQL Injection means injecting/inserting SQL code in a query via user-inputted data. It can occur in any applications using relational databases like Oracle, MySQL, PostgreSQL and SQL Server.
What is SQL injection example?
Some common SQL injection examples include: Retrieving hidden data, where you can modify an SQL query to return additional results. Subverting application logic, where you can change a query to interfere with the application’s logic. UNION attacks, where you can retrieve data from different database tables.
What happens SQL injection?
SQL injection attacks occur when a web application does not validate values received from a web form, cookie, input parameter, etc., before passing them to SQL queries that will be executed on a database server. … SQL injection attack risk is usually very high and the consequences are severe.
What is SQL injection and how does it work?
SQL injection (SQLi) is a type of cyberattack against web applications that use SQL databases such as IBM Db2, Oracle, MySQL, and MariaDB. As the name suggests, the attack involves the injection of malicious SQL statements to interfere with the queries sent by a web application to its database.How is SQL injection prevention?
The only sure way to prevent SQL Injection attacks is input validation and parametrized queries including prepared statements. The application code should never use the input directly. The developer must sanitize all input, not only web form inputs such as login forms.
What is SQL injection quizlet?
SQL injection is a code injection technique, used to attack data-driven applications, in which nefarious SQL statements are inserted into an entry field for execution (e.g. to dump the database contents to the attacker).
What is SQL injection in hibernate?
SQL injection refers to the act of someone inserting a MySQL statement to be run on your database without your knowledge. Injection usually occurs when you ask a user for input, like their name, and instead of a name they give you a MySQL statement that you will unknowingly run on your database.
What is HTML injection?
Hypertext Markup Language (HTML) injection is a technique used to take advantage of non-validated input to modify a web page presented by a web application to its users. … When applications fail to validate user data, an attacker can send HTML-fomatted text to modify site content that gets presented to other users.What is XML injection?
XML injection manipulates or compromises the logic of an XML application or service. The injection of unintended XML content and/or structures into an XML message can alter the intended logic of an application, and XML Injection can cause the insertion of malicious content into resulting messages/documents.
What causes SQL injection?The three root causes of SQL injection vulnerabilities are the combining of data and code in dynamic SQL statement, error revealation, and the insufficient input validation.
Article first time published onWhy is SQL injection so common?
Trusting Input “Trust without verification is one key reason why SQL injection is still so prevalent,” says Dwayne Melancon, chief technology officer for Tripwire. “Some application developers simply don’t know any better; they inadvertently write applications that blindly accept any input without validation.”
What is SQL injection error?
Error-based SQL injection is an In-band injection technique where the error output from the SQL database is used to manipulate the data inside the database. … You can force data extraction by using a vulnerability in which the code will output a SQL error rather than the required data from the server.
What does SQL stand for?
SQL (pronounced “ess-que-el”) stands for Structured Query Language. SQL is used to communicate with a database. According to ANSI (American National Standards Institute), it is the standard language for relational database management systems.
What is the purpose of an SQL injection Mcq?
Explanation: SQL injection is a code injection technique, used to attack data-driven applications.
How the SQL injection affects a system's performance?
The impact SQL injection can have on a business is far-reaching. A successful attack may result in the unauthorized viewing of user lists, the deletion of entire tables and, in certain cases, the attacker gaining administrative rights to a database, all of which are highly detrimental to a business.
Can SQL injections be detected?
SQL Injection has become a common issue with database-driven web sites. The flaw is easily detected, and easily exploited, and as such, any site or software package with even a minimal user base is likely to be subject to an attempted attack of this kind.
What are 2 methods or steps that can be taken to prevent SQL injection attacks?
- Validate User Inputs. …
- Sanitize Data by Limiting Special Characters. …
- Enforce Prepared Statements and Parameterization. …
- Use Stored Procedures in the Database. …
- Actively Manage Patches and Updates. …
- Raise Virtual or Physical Firewalls. …
- Harden Your OS and Applications.
What are the solution for injection attacks?
How to prevent SQL injection attacks. Avoid placing user-provided input directly into SQL statements. Prefer prepared statements and parameterized queries , which are much safer. Stored procedures are also usually safer than dynamic SQL.
What is difference between HQL and SQL?
Differences between SQL and HQL: SQL is based on a relational database model whereas HQL is a combination of object-oriented programming with relational database concepts. SQL manipulates data stored in tables and modifies its rows and columns. HQL is concerned about objects and its properties.
Is SQL injection possible with JPA?
Yes, it is possible. It depends on the way you implement. Have a look at Preventing injection in JPA query language.
What is JPA?
The Java Persistence API (JPA) is a specification of Java. It is used to persist data between Java object and relational database. JPA acts as a bridge between object-oriented domain models and relational database systems. As JPA is just a specification, it doesn’t perform any operation by itself.
How do you string two SQL injection queries together quizlet?
How do you string two SQL injection queries together? You would end the first SQL statement with a closing quote (if needed) , then a semicolon (to denote the end of the first query), then the second query with its ending semicolon, and finally a — for the comment.
Why would a hacker deliberately inject SQL code that would generate errors?
In this SQL injection attack, an attacker sends an incorrect query to the database intentionally to generate an error message that may be helpful in performing further attacks. … This type of injections allows an attacker to bypass blacklisting, remove spaces, obfuscate, and determine database versions.
Why would an attacker send 1 1 to a remote server?
Why would an attacker send 1=1 to a remote server? … 1=1 is always true, and therefore causes the server perform the action associated with a true response.
What is XML injection example?
XML Injection is an attack technique used to manipulate or compromise the logic of an XML application or service. One example of this is where XML message payloads that contain a CDATA field can be used to inject illegal characters/content that are ignored by the XML parser. …
What is XML used for?
The Extensible Markup Language (XML) is a simple text-based format for representing structured information: documents, data, configuration, books, transactions, invoices, and much more. It was derived from an older standard format called SGML (ISO 8879), in order to be more suitable for Web use.
What can cause XML injection?
Description: XML injection XML or SOAP injection vulnerabilities arise when user input is inserted into a server-side XML document or SOAP message in an unsafe way. It may be possible to use XML metacharacters to modify the structure of the resulting XML.
What is URL injection?
URL Injection occurs when a hacker has created/injected new pages on an existing website. These pages often contain code that redirects users to other sites or involves the business in attacks against other sites. These injections can be made through software vulnerabilities, unsecured directories, or plug-ins.
What is CSV injection?
CSV Injection, also known as Formula Injection, occurs when websites embed untrusted input inside CSV files. When a spreadsheet program such as Microsoft Excel or LibreOffice Calc is used to open a CSV, any cells starting with = will be interpreted by the software as a formula.
What is CSS injection?
A CSS Injection vulnerability involves the ability to inject arbitrary CSS code in the context of a trusted web site which is rendered inside a victim’s browser. … This vulnerability occurs when the application allows user-supplied CSS to interfere with the application’s legitimate stylesheets.
What is database injection?
An SQL injection is a type of cyber attack in which a hacker uses a piece of SQL (Structured Query Language) code to manipulate a database and gain access to potentially valuable information.