What is principal Kerberos

Emma Valentine
Published Mar 20, 2026
A Kerberos Principal represents a unique identity in a Kerberos system to which Kerberos can assign tickets to access Kerberos-aware services. Principal names are made up of several components separated by the “/” separator. You can also specify a realm as the last component of the name by using the “@” character.
What is principal and Keytab in Kerberos?
The Kerberos Keytab file contains mappings between Kerberos Principal names and DES-encrypted keys that are derived from the password used to log into the Kerberos Key Distribution Center (KDC).
What is Kerberos and how it works?
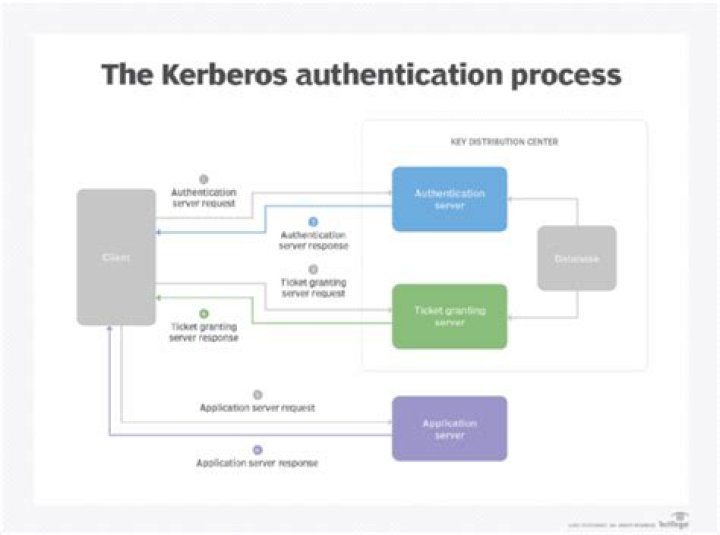
Under Kerberos, a client (generally either a user or a service) sends a request for a ticket to the Key Distribution Center (KDC). The KDC creates a ticket-granting ticket (TGT) for the client, encrypts it using the client’s password as the key, and sends the encrypted TGT back to the client.
How do you get principal name in Kerberos?
- Configure NTP. First, it is quite common to have NTP clients configured in every system AD server, Apache server and Tomcat server. …
- Create an AD principal for the server. …
- Install and configure Kerberos on Apache server. …
- Install and configure mod_auth_kerb. …
- AJP Configuration. …
- Web app authentication.
Where is Keytab?
keytab , by default. On application servers that provide Kerberized services, the keytab file is located at /etc/krb5/krb5. keytab , by default. A keytab is analogous to a user’s password.
How do I find service principal name?
To view a list of the SPNs that a computer has registered with Active Directory from a command prompt, use the setspn –l hostname command, where hostname is the actual host name of the computer object that you want to query.
How do you add principal and Keytab in Kerberos?
- Log on as theKerberos administrator (Admin) and create a principal in the KDC. You can use cluster-wide or host-based credentials. …
- Obtain the key of the principal by running the subcommand getprinc principal_name .
- Create the keytab files, using the ktutil command:
Why is Kerberos used?
Kerberos has two purposes: security and authentication. … In addition, it is necessary to provide a means of authenticating users: any time a user requests a service, such as mail, they must prove their identity. This is done with Kerberos, and this is why you get your mail and no one else’s.What does Ntlm mean?
Windows New Technology LAN Manager (NTLM) is a suite of security protocols offered by Microsoft to authenticate users’ identity and protect the integrity and confidentiality of their activity.
What are the key benefits of Kerberos?- Faster authentication. The Kerberos protocol uses a unique ticketing system that provides faster authentication: …
- Mutual authentication. Kerberos supports mutual authentication. …
- Kerberos is an open standard. …
- Support for authentication delegation. …
- Support for the smart card logon feature.
What are the 3 main parts of Kerberos?
Kerberos has three parts: a client, server, and trusted third party (KDC) to mediate between them. Clients obtain tickets from the Kerberos Key Distribution Center (KDC), and they present these tickets to servers when connections are established.
What is krb5 Keytab file?
The Keytab File All Kerberos server machines need a keytab file, called /etc/krb5. keytab , to authenticate to the KDC. The keytab file is an encrypted, local, on-disk copy of the host’s key. … The keytab file should be readable only by root, and should exist only on the machine’s local disk.
What is Kerberos credential cache?
A credential cache (or “ccache”) holds Kerberos credentials while they remain valid and, generally, while the user’s session lasts, so that authenticating to a service multiple times (e.g., connecting to a web or mail server more than once) doesn’t require contacting the KDC every time.
What is Klist command?
Description. The klist command displays the contents of a Kerberos credentials cache or key table.
What is Kvno?
The key version number , commonly abbreviated as kvno, distinguishes between different encryption keys that are stored for a given principal. For example, if a user changes his password, then his principal has a new encryption key associated with it.
How do I create a .keytab file?
- Log in to any cluster VM.
- From the command line, type. ktutil. …
- Type the following command: addent -password -p <user name> -k 1 -e RC4-HMAC. …
- When prompted, enter the password for the Kerberos principal user.
- Type the following command to create a keytab: …
- Type.
What is Ktutil command?
The ktutil command is an interactive command-line interface utility for managing the keylist in keytab files. You must read in a keytab’s keylist before you can manage it. Also, the user running the ktutil command must have read/write permissions on the keytab.
How do I create a gMSA account?
- Create group of NETID computers to associate with gMSA.
- Create gMSA & associate with group from step #1.
- Install the gMSA on the computer(s)
- Configure the service, IIS app pool, or scheduled task to use the gMSA.
What does a service principal name SPN consist of?
A Service Principal Name (SPN) is a name in Active Directory that a client uses to uniquely identify an instance of a service. An SPN combines a service name with a computer and user account to form a type of service ID.
What is service principal name in Azure?
An Azure Active Directory (Azure AD) service principal is the local representation of an application object in a single tenant or directory. It functions as the identity of the application instance. Service principals define who can access the application, and what resources the application can access.
Is NTLMv2 salted?
Is the NTLMv2 hash even salted? NTLM is designed to do authentication over an unencrypted channel with a shared secret (password). … To answer your question: NTLM is unsalted, and NTLMv2 adds a salt, which is exchanged in the messaging.
What is the difference between NTLMv1 and NTLMv2?
The difference lies in the challenge and in the way the challenge is encrypted: While NTLMv2 provides a variable-length challenge, the challenge used by NTLMv1 is always a sixteen byte random number. NTLMv1 uses a weak DES algorithm to encrypt the challenge with the user’s hash. … NTLMv2 uses HMAC-MD5 instead.
What is NetNTLM?
NetNTLM is Windows’ challenge-response protocol that is mainly used where Kerberos is not supported. … There are two versions of the NetNTLM authentication protocol, and both are vulnerable to certain attacks.
What needs Kerberos?
Kerberos builds on symmetric-key cryptography and requires a trusted third party, and optionally may use public-key cryptography during certain phases of authentication. Kerberos uses UDP port 88 by default.
What is the difference between SAML and Kerberos?
SAML is just a standard data format for exchanging authentication data securely using XML Schema, XML signature, XML encryption and SOAP. You would typically use it for a web SSO (single sign on). … Kerberos requires that the user it is authenticating is in the kerberos domain.
Why Kerberos is secure?
Kerberos is far from obsolete and has proven itself an adequate security-access control protocol, despite attackers’ ability to crack it. The primary advantage of Kerberos is the ability to use strong encryption algorithms to protect passwords and authentication tickets.
Are there any known weaknesses in Kerberos?
The Kerberos protocol is not as resistant to penetration as it should be. A number of weaknesses are apparent; the most serious is its use of an authen- ticator to prevent replay attacks. The authenticator relies on use of a timestamp to guard against reuse. This is problematic for several reasons.
What are the Kerberos limitations?
Biggest lose: assumption of secure time system, and resolution of synchronization required. Could be fixed by challenge-response protocol during auth handshake. Password guessing: no authentication is required to request a ticket, hence attacker can gather equivalent of /etc/passwd by requesting many tickets.
How is Kerberos managed in Windows 2000 system?
Windows 2000 implements Kerberos version 5 with extensions for public key authentication. The Kerberos client is implemented as a security provider through the Security Support Provider Interface. Initial authentication is integrated with the Winlogon single sign-on architecture.
Why is it called Kerberos?
Kerberos was developed for Project Athena at the Massachusetts Institute of Technology (MIT). The name was taken from Greek mythology; Kerberos (Cerberus) was a three-headed dog who guarded the gates of Hades.
What are the two components of Kerberos?
Kerberos has the following components: Principal—Client (user) or service. Realm—A logical Kerberos network. Ticket—Data that authenticates a principal’s identity.