What is configuration identification

Emma Valentine
Published Mar 08, 2026
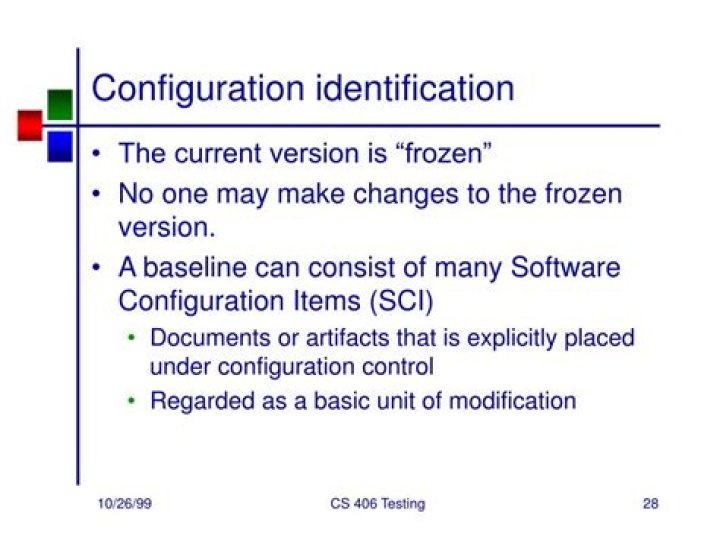
Configuration identification is the process of identifying the attributes that define every aspect of a configuration item. A configuration item is a product (hardware and/or software) that has an end-user purpose. These attributes are recorded in configuration documentation and baselined.
What is configuration item identification?
Configuration identification is the selection and specification of the following: Products delivered to the customer. … Acquired products. Tools and other capital assets of the project’s work environment. Other items used in creating and describing these work products.
What is configuration verification and audit?
Verification and auditing is responsible for ensuring that information in Configuration Management is accurate and that all Configuration Items (CIs) are identified and recorded in Configuration Management. The process can be conducted manually, or by using automated inventory and discovery tools.
Which is configuration identification aspect of configuration management system?
Configuration identification: Involves breaking down the project and creating a referencing system for each item. Configuration control: Ensures that all changes to configuration items are controlled. Configuration control of specifications and test plans is vital for quality control to be effective.What is meant by configuration item?
A configuration item (CI) is any service component, infrastructure element, or other item that needs to be managed in order to ensure the successful delivery of services. Each CI has several characteristics: A classification, or type, which indicates what kind of item it is.
What is CI in ITIL?
A Configuration Item (CI) is an ITIL term used for a component in the infrastructure or item associated with the infrastructure of a company. CIs are controlled by the Configuration Management application.
What is the purpose of configuration item?
Configuration items help in identifying the components of a system. In configuration management it helps in tracking the granular changes and helps in system maintenance as well for any possible error detection.
Who is responsible for configuration identification activity?
Configuration Identification (process ST 3.2) In the Configuration Identification process, the Configuration Administrator selects Configuration Items (CIs), records their identifying characteristics, and assigns unique identifiers to the selected items.What is configuration example?
The definition of configuration is the way parts are arranged to work together. … When you try to set up your computer hardware and software to work the way you want such as adding a wireless mouse and keyboard, this is an example of configuration.
What are the main purpose of configuration management?Configuration management is a process for maintaining computer systems, servers, and software in a desired, consistent state. It’s a way to make sure that a system performs as it’s expected to as changes are made over time.
Article first time published onWhat is FCA and PCA?
Simply put, a FCA is a financially focused review while a PCA is a more technical condition tool. A few other services, including forensic reviews, reserve studies, construction QC checks, are also commonly confused with FCAs and PCAs, so it’s essential to get them straight.
Who performs configuration audit?
Configuration audits may be conducted by the software quality assurance, the configuration management or the verification and validation functions.
How do I audit CMDB?
- Open a CI, as described in Using search.
- In the navigation pane, select Functions > CMDB Audits.
- On the View Instance History form, select a history entry, and click View.
What is the difference between asset and CI?
The Fundamental Difference As per ITIL, a CI is a component or service item that needs to be managed in order to deliver services, and an asset is a resource or capability that contributes to the delivery of the services. Which means that an item can be tracked as both a CI and an asset if required.
What is CI in remedy?
A configuration item (CI) is a physical, logical, or conceptual entity that is part of your IT environment and has configurable attributes. Some CI types are virtual, while others are physical and include hardware and software.
What are the three key tables in the CMDB?
- The Base Configuration Item [cmdb] table, which is the core CMDB table for non IT CIs (descending classes are non IT CIs).
- The core Configuration Item [cmdb_ci] table, which stores the basic attributes of all the CIs.
Is laptop a configuration item?
Laptops / Computers Labeling laptops and computers as configuration items (CIs) makes for easy storage of records in a CMDB.
Is software a configuration item?
Definition(s): Item or aggregation of hardware, software, or both, that is designated for configuration management and treated as a single entity in the configuration management process.
What are the important configuration items?
Examples of Configuration Items include software and applications, locations and offices, employees and customers, documentation, hardware and companies, and even your incidents, changes and customers.
What is the difference between CMDB and CMS?
Definition: The Configuration Management System (CMS) is a set of tools and data that is used for collecting, storing, managing, updating, analyzing and presenting data about all configuration items and their relationships. A CMS may manage more than one physical Configuration Management Databases (CMDB).
What is the difference between DML and CMDB?
CMDB is the main database. It may be implemented as a software solution or even can be maintained in excel sheet (in case of small office). Even some may track it in a physical ledger book (old mills). DML can also be digitalized or can be in physical form.
What is ITSM system?
IT service management — often referred to as ITSM — is simply how IT teams manage the end-to-end delivery of IT services to customers. This includes all the processes and activities to design, create, deliver, and support IT services.
What configuration consists of?
Configuration is the manner in which components are arranged to make up the computer system. Configuration consists of both hardware and software components. Sometimes, people specifically point to hardware arrangement as hardware configuration and to software components as software configuration.
What is configuration process?
The Configuration Management process ensures that selected components of a complete IT service, system, or product (the Configuration Item) are identified, baselined, and maintained and that changes to them are controlled.
What is configuration of a laptop?
A configuration is the way a system is set up, or the assortment of components that make up the system. … For instance, a typical configuration for a laptop PC consists of 8GB or 16GB (gigabytes) main memory, multiple USB ports, a hard disk or solid-state drive (SSD), a wireless card, and an operating system.
What is CM2 configuration management?
CM2 (formerly CMII) is the global enterprise standard for enterprise change and configuration management. Since 1986, CM2 has provided the most robust comprehensive methodology for managing the configuration of a product, system, and/or service throughout its life.
Why baseline is important during configuration identification activity?
“A baseline identifies an agreed-to description of the attributes of a {system} at a point in time and provides a known configuration to which changes are addressed.” Establishing baselines and managing changes to baselines are the key functions of configuration management.
What is a configuration document?
The term configuration documentation characterizes the information that defines the performance, functional and physical attributes of a product.
What is configuration management example?
A telecom firm maintains a configuration management database that includes relationships between components. … For example, if a router goes down the firm has immediate access to a list of impacted services and customers. The company phones customers to tell them their service is down before they typically notice.
What is the first step of configuration management?
The first step in the process is planning and identification. In this step, the goal is to plan for the development of the software project and identify the items within the scope.
Who is responsible for configuration management?
Project Manager – will produce the Configuration Management Plan and include within the Project Management plan. Responsible for ensuring all who work on the project are aware of the Configuration Management Plan and understand how the plan works.