What is CIA triad concept

William Taylor
Published Feb 23, 2026
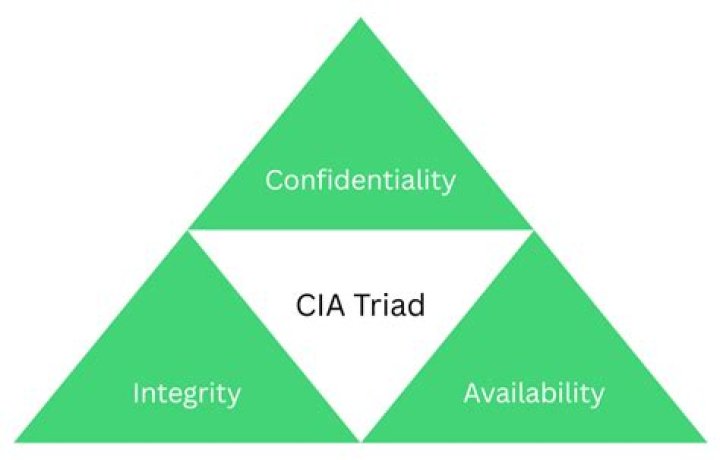
Confidentiality, Integrity, and Availability. These are the three core components of the CIA triad, an information security model meant to guide an organization’s security procedures and policies.
When was the CIA triad made?
The paper recognized that commercial computing had a need for accounting records and data correctness. Even though it is not as easy to find an initial source, the concept of availability became more widespread one year later in 1988. By 1998, people saw the three concepts together as the CIA triad.
Why CIA triad is important?
CIA triad is essential in cybersecurity as it provides vital security features, helps in avoiding compliance issues, ensures business continuity, and prevents reputational damage to the organization.
What are the three principles of the CIA triad?
As a part of an information security training, and any attempt to minimise potential risks, there are three principles upon which professionals typically focus: Confidentiality, Integrity and Availability. This is known as the CIA Triad.What part of the CIA Triad has been broken?
Integrity has been broken. This is because the trust between the two parties has been compromised. Kim takes her college admissions test and is waiting to get her results by email. By accident, Kim’s results are sent to Karen.
How is CIA triad implemented?
- Categorize data and assets being handled based on their privacy requirements.
- Require data encryption and two-factor authentication to be basic security hygiene.
- Ensure that access control lists, file permissions and white lists are monitored and updated regularly.
What is the CIA Triad and why is it important for cybersecurity?
The three letters in “CIA triad” stand for confidentiality, integrity, and availability. The CIA triad is a common, respected model that forms the basis for the development of security systems and policies.
Who is responsible for adherence of information security?
Everyone is responsible for the security of information within a business. From the owner down to a summer intern, by being involved in the business and handling data, you have to make sure to keep information secure and remain vigilant to security threats like hackers.What item is not component of the CIA triad?
A final important principle of information security that doesn’t fit neatly into the CIA triad is non-repudiation, which essentially means that someone cannot falsely deny that they created, altered, observed, or transmitted data.
What are the four elements of security?- Protection, Detection, Verification & Reaction.
- ‘Protection’ is the physical barrier, such as walls and fences, which separates your property from the rest of the world.
Which of the following of the CIA Triad ensures that the information is correct and no unauthorized person has altered it?
Explanation: The CIA triad consists of confidentiality, integrity, and availability. … Explanation: The goal of integrity is to ensure that unauthorized users cannot modify data and that authorized users are not making improper or unauthorized modifications of the data. You just studied 149 terms!
Is broadly known as CIA Triad?
These three letters stand for confidentiality, integrity, and availability, otherwise known as the CIA triad. Together, these three principles form the cornerstone of any organization’s security infrastructure; in fact, they (should) function as goals and objectives for every security program.
Who are the threat agents?
- A Threat Actor or Threat Agent is a party that is responsible for, or attempts to bring about, harm to an organization. …
- Threat actors can be persons, groups, or entities and they are sometimes referred to as malicious actors.
Is Ransomware a data breach?
The presence of ransomware (or any malware) is a security incident under HIPAA that may also result in an impermissible disclosure of PHI in violation of the Privacy Rule and a breach, depending on the facts and circumstances of the attack.
How do you get into CIA?
- Categorize data and assets being handled based on their privacy requirements.
- Require data encryption and two-factor authentication to be basic security hygiene.
- Ensure that access control lists, file permissions and white lists are monitored and updated regularly.
What does the term human firewall mean?
Let’s establish a quick human firewall definition. The concept is quite simple. It refers to the people at your organization, and their potential to become a one-stop cyber-crime fighting machine. … It involves establishing a group of people within your organization who promote and carry out cybersecurity best practice.
How does CIA triad impact security efforts in the real world?
It guides an organization’s efforts towards ensuring data security. The three principles—confidentiality, integrity, and availability which is also the full for CIA in cybersecurity, form the cornerstone of a security infrastructure. In fact, it is ideal to apply these principles to any security program.
What aspect of the CIA triad do DOS and DDoS attacks threaten?
DDoS attacks are one of the most effective ways for malicious actors to violate availability, the third of three foundational security principles—confidentiality, integrity, and availability—in what is known as the CIA triad.
What is firewall used for?
A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules. Firewalls have been a first line of defense in network security for over 25 years.
What is AAA in cyber security?
Authentication, authorization, and accounting (AAA) is a security framework that controls access to computer resources, enforces policies, and audits usage.
Why would a hacker use a proxy server?
Why Would A Hacker Use A Proxy Server? … To Create A Ghost Server On The Network. To Hide Malicious Activity On The Network. To Obtain A Remote Access Connection.
Who is responsible for data privacy?
Your company has a responsibility to safeguard customer data, including personal information, just as it does other company data, such as proprietary information and trade secrets. A company’s data, next to its employees, is the organization’s most essential asset.
Who are the targets of modern day hackers?
Small and medium business are the top target for cyberattacks. Unlike large corporations who have the money and resources to pay for cybersecurity and upgrade their network match the latest hacker tricks, small businesses do not have that same luxury” and hackers know it.
Who bears the responsibility for information security in an organization?
Chief Information Security Officer: The CISO normally serves as the organization’s senior agency information security officer (SAISO) as required by FISMA. The CISO’s primary responsibility is information security, and he or she carries out the FISMA-related functions assigned to the CIO.
What is an InfoSec blueprint?
Answer: The InfoSec blueprint is the detailed plan for the complete design, selection, and implementation of all subsequent security controls, including InfoSec policies, security education and training programs, and technological controls. It includes sequenced steps and planned timeframes for each component.
What is CIA rating?
The value of levels for CIA are as follows: A rating of 3 is high, 2 is medium and 1 is low. The value of the information asset is determined by the sum of the three (C + I + A) attributes.
In which way security can be attacked?
Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks. Man-in-the-middle (MitM) attack. Phishing and spear phishing attacks. Drive-by attack.
Which aspect of the CIA triad would cover ensuring information non repudiation and authenticity?
Integrity refers to maintaining the accuracy, and completeness of data. In other words, it is about protecting data from being modified by unauthorized parties, accidentally by authorized parties, or by non-human-caused events such as electromagnetic pulse or server crash.
Which of the following ensures that information has not been altered in any unauthorized ways by any means?
Integrity is the ability to ensure that a system and its data has not suffered unauthorized modification. Integrity protection protects not only data, but also operating systems, applications and hardware from being altered by unauthorized individuals.
Can you have confidentiality without integrity?
Without integrity no system can provide confidentiality. … Other than that to be able to enforce confidentiality, at least you need the integrity of the hardware the system is running upon. If there is no integrity, then there is no guarantee of secure operations on that system, which compromises confidentiality.
What are the 12 categories of threats?
- Spoofing of user identity.
- Tampering.
- Repudiation.
- Information disclosure (privacy breach or Data leak)
- Denial of Service (D.o.S.)
- Elevation of privilege.