What is an AWS IAM policy

Christopher Lucas
Published Feb 17, 2026
IAM policies define permissions for an action regardless of the method that you use to perform the operation. For example, if a policy allows the GetUser action, then a user with that policy can get user information from the AWS Management Console, the AWS CLI, or the AWS API.
What is IAM policy vs role?
Hi Sonal, IAM roles define the set of permissions for making AWS service request whereas IAM policies define the permissions that you will require.
How do I write AWS IAM policy?
To create the policy for your test user Sign in to the IAM console at / with your user that has administrator permissions. In the navigation pane, choose Policies. In the content pane, choose Create policy. Choose the JSON tab and copy the text from the following JSON policy document.
What can be found in IAM policy?
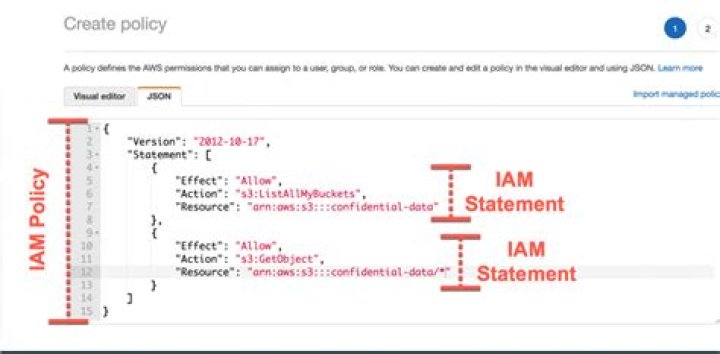
IAM Policy Examples In this policy, there are four major JSON elements: Version, Effect, Action, and Resource. … In this policy, the Effect is “Allow” , which means you’re providing access to a particular resource. The Action element describes the type of action that should be allowed or denied.How do I create AWS IAM policy?
To create your own IAM policy Sign in to the AWS Management Console and open the IAM console at . Choose Policies, and then choose Create Policy. If a Get Started button appears, choose it, and then choose Create Policy. Next to Create Your Own Policy, choose Select.
How do I find my IAM role in AWS?
- Click Amazon DynamoDB in the Select service dropdown list.
- Click Select All to simulate all DynamoDB actions for your role.
- Click RDS in the Select service dropdown list.
- Click Select All to test all RDS actions for your role.
How does AWS IAM evaluate a policy?
When an IAM entity (user or role) requests access to a resource within the same account, AWS evaluates all the permissions granted by the identity-based and resource-based policies. … If an action is allowed by an identity-based policy, a resource-based policy, or both, then AWS allows the action.
How do I validate AWS IAM policy?
- Test policies that are attached to IAM users, user groups, or roles in your AWS account. …
- Test and troubleshoot the effect of permissions boundaries on IAM entities.
What is the role of CloudWatch in AWS?
Amazon CloudWatch is a monitoring and management service that provides data and actionable insights for AWS, hybrid, and on-premises applications and infrastructure resources. … You can use CloudWatch Container Insights to monitor, troubleshoot, and alert your containerized applications and microservices.
What is effect in AWS policy?The Effect element is required and specifies whether the statement results in an allow or an explicit deny. Valid values for Effect are Allow and Deny . “Effect”:”Allow” By default, access to resources is denied. To allow access to a resource, you must set the Effect element to Allow .
Article first time published onWhat is policy simulator?
In the policy simulator, administrators can now create a permissions boundary policy, assign it to an IAM principal with existing IAM policies and then simulate an AWS service action to evaluate the impact of the permissions boundary policy on the IAM principal’s effective permissions for the simulated AWS service …
What is the difference between an IAM role and an IAM user?
An IAM user has permanent long-term credentials and is used to directly interact with AWS services. An IAM role does not have any credentials and cannot make direct requests to AWS services. IAM roles are meant to be assumed by authorized entities, such as IAM users, applications, or an AWS service such as EC2.
How do I assume AWS role?
You can assume a role by calling an AWS CLI or API operation or by using a custom URL. The method that you use determines who can assume the role and how long the role session can last. ¹ Using the credentials for one role to assume a different role is called role chaining.
How do I check AWS permissions?
- In the navigation pane, choose Users.
- Choose the name of the user whose permissions boundary you want to change.
- Choose the Permissions tab. …
- Select the policy that you want to use for the permissions boundary.
What is CloudWatch and how it works?
Amazon CloudWatch is basically a metrics repository. An AWS service—such as Amazon EC2—puts metrics into the repository, and you retrieve statistics based on those metrics. … You can configure alarm actions to stop, start, or terminate an Amazon EC2 instance when certain criteria are met.
Is AWS serverless CloudWatch?
Improve operational performance and resource optimization You can also use CloudWatch Events for serverless to trigger workflows with services like AWS Lambda, Amazon SNS, and AWS CloudFormation.
What is CloudTrail and CloudWatch?
Amazon Cloudwatch is a monitoring service that gives you visibility into the performance and health of your AWS resources and applications, whereas AWS Cloudtrail is a service that logs AWS account activity and API usage for risk auditing, compliance and monitoring.
What is AWS access analyzer?
AWS IAM Access Analyzer helps you identify the resources in your organization and accounts, such as Amazon S3 buckets or IAM roles, shared with an external entity. This lets you identify unintended access to your resources and data, which is a security risk.
Which IAM policy provides permissions to resolve issues with AWS?
You can grant permission to IAM users to access the AWS Support Center by attaching a managed policy to the IAM user, group, or role. Follow the instructions to use a managed policy as a permissions policy for an identity (AWS Management Console), and then choose the AWSSupportAccess policy.
How do I find my AWS password policy?
You can navigate to the AWS IAM console then click on Account settings that will state whether or not a password policy has been set for the account.
What is not action in IAM policy?
NotAction is an advanced policy element that explicitly matches everything except the specified list of actions. Using NotAction can result in a shorter policy by listing only a few actions that should not match, rather than including a long list of actions that will match.
What is Sid in IAM policy?
You can provide an optional identifier, Sid (statement ID) for the policy statement. You can assign a Sid value to each statement in a statement array. In services that let you specify an ID element, such as SQS and SNS, the Sid value is just a sub-ID of the policy document ID.
What is principal in AWS policy Generator?
Principal. A principal is a person or application that can make a request for an action or operation on an AWS resource. The principal is authenticated as the AWS account root user or an IAM entity to make requests to AWS.
What is AWS userid?
aws:userid This value is the unique ID for the current user—see the chart that follows. aws:username This is a string containing the friendly name of the current user—see the chart that follows. ec2:SourceInstanceARN This is the Amazon Resource Name (ARN) of the Amazon EC2 instance from which the request is made.
What is an instance profile AWS?
An instance profile is a container for an IAM role that you can use to pass role information to an EC2 instance when the instance starts.
What is the difference between instance profile and IAM role?
An Instance Profile is a container for a single IAM Role. A typical convention is to create an IAM Role and an Instance Profile of the same name for clarity. An EC2 Instance cannot be assigned a Role directly, but it can be assigned an Instance Profile which contains a Role.
Which of the following are best practices of IAM?
- Lock away your AWS account root user access keys.
- Use roles to delegate permissions.
- Grant least privilege.
- Get started using permissions with AWS managed policies.
- Validate your policies.
- Use customer managed policies instead of inline policies.
- Use access levels to review IAM permissions.
Can an IAM role assume another role?
To allow an IAM Role to assume another Role, we need to modify the trust relationship of the role that is to be assumed. This process varies depending if the roles exist within the same account or if they’re in separate accounts.
Do IAM roles expire?
You can easily extend the maximum session duration for an IAM role to up to 12 hours using the IAM console or CLI. … Once you increase the maximum session duration, users and applications assuming the IAM role can request temporary, short-term credentials that expire when the IAM role session expires.
What is Assume role policy?
To use the temporary security credentials to access the AWS resources, both the IAM user and IAM role require policies. The policy specifies the AWS resource that the IAM user can access and the actions that the IAM user can perform. …
How do I assign an IAM to a user?
- In the navigation pane of the console, choose Roles and then choose Create role.
- Choose the Another AWS account role type.
- For Account ID, type the AWS account ID to which you want to grant access to your resources.