What is a Web based attack

Christopher Lucas
Published Mar 17, 2026
A Web application attack is any attempt by a malicious actor to compromise the security of a Web-based application. Web application attacks may target either the application itself to gain access to sensitive data, or they may use the application as a staging post to launch attacks against users of the application.
Which of the following is a web-based attacks?
Web-based attacks Example- SQL Injection, code Injection, log Injection, XML Injection etc. DNS Spoofing is a type of computer security hacking.
What are the different types of web attacks?
- Malware. Malware is a term used to describe malicious software, including spyware, ransomware, viruses, and worms. …
- Phishing. …
- Man-in-the-middle attack. …
- Denial-of-service attack. …
- SQL injection. …
- Zero-day exploit. …
- DNS Tunneling.
How does web attack work?
Un-targeted cyber attacks phishing – sending emails to large numbers of people asking for sensitive information (such as bank details) or encouraging them to visit a fake website. water holing – setting up a fake website or compromising a legitimate one in order to exploit visiting users.Why are web-based applications vulnerable?
Why are web applications so vulnerable to attacks? Web applications are very vulnerable to attacks because, by design, they cannot be protected by firewalls. They must be available to everyone, all the time, unless they are on an intranet. Malicious hackers can, therefore, try to exploit them easily.
Is virus a web based attack?
Internet-based threats expose people and computer systems to harm online. A broad scope of dangers fits into this category, including well-known threats like phishing and computer viruses. However, other threats, like offline data theft, can also be considered part of this group.
What are the four types of cyber attacks?
- Malware. Malware is a type of application that can perform a variety of malicious tasks. …
- Phishing. …
- Man-in-the-middle attack (MITM) …
- Distributed Denial-of-Service (DDoS) attack. …
- SQL injection. …
- Zero-day exploit. …
- DNS Tunnelling. …
- Business Email Compromise (BEC)
How are cyber attacks executed?
Cyber attacks often happen in stages, starting with hackers surveying or scanning for vulnerabilities or access points, initiating the initial compromise and then executing the full attack — whether it’s stealing valuable data, disabling the computer systems or both.Which of the following would protect against web based attacks?
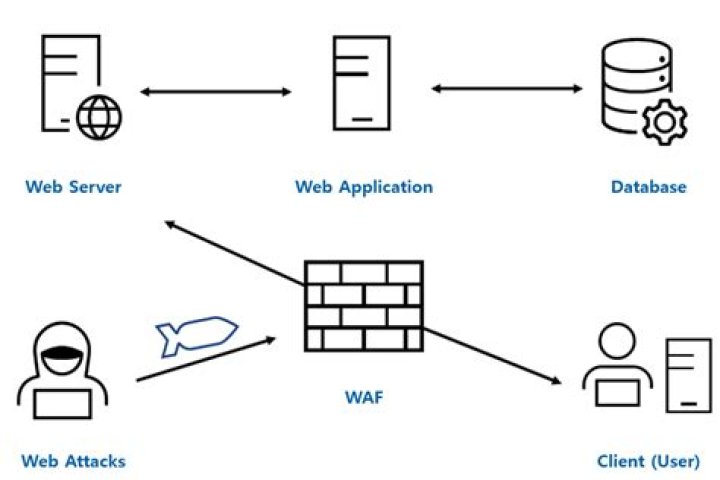
You can protect your website against XSS attacks by setting up a web application firewall (WAF). WAF acts as a filter that identifies and blocks any malicious requests to your website. Usually, web hosting companies already have WAF in place when you purchase their service, but you can also set it up yourself.
Which of the following are examples of on Path attacks?In addition to websites, these attacks can target email communications, DNS lookups, and public WiFi networks. Typical targets of on-path attackers include SaaS businesses, ecommerce businesses, and users of financial apps.
Article first time published onWhy would a hacker use a proxy server?
To hide malicious activity on the network. Explanation – Proxy servers exist to act as an intermediary between the hacker and the target and servces to keep the hacker anonymous tot he network.
What are three of the most common web vulnerabilities?
- SQL Injections. …
- Cross Site Scripting (XSS) …
- Broken Authentication & Session Management. …
- Insecure Direct Object References. …
- Security Misconfiguration. …
- Cross-Site Request Forgery (CSRF)
What is the most common web security vulnerability?
Cross-Site Scripting (XSS) is one of the most common vulnerabilities of web applications. It’s a type of attack which comprises of code embedding into a legitimate website by using the user input fields.
Are web Apps secure?
A web application firewall or WAF helps protect a web application against malicious HTTP traffic. By placing a filtration barrier between the targeted server and the attacker, the WAF is able to protect against attacks like cross site forgery, cross site scripting and SQL injection.
Where do most cyber attacks come from?
1.China41 percent (of the world’s attack traffic)2.U.S.10 percent3.Turkey4.7 percent4.Russia4.3 percent5.Taiwan3.7 percent
How do malware attacks occur?
How does malware work? Malware typically infects a machine by tricking users into clicking and/or installing a program that they shouldn’t from the Internet.
Which countries are most often the victims of malware attacks?
The United States were the most frequently targeted country, accounting for almost half of the global total malware attacks.
Are common threat to computer and the internet as a whole?
Computer Viruses Computer viruses are the most common among internet security threats out there. … The goal of viruses is to infect your other computers and networked systems. One of the basic steps to protecting your computers from viruses is by setting up a firewall.
How is malware deployed?
Malware prevention Still, most types are deployed via phishing emails. The best means of prevention is ensuring you use spam filters to the max. In addition to using spam filters, look at using email programs that preemptively scan attachments.
What is spyware attack?
Spyware is a type of malicious software — or malware — that is installed on a computing device without the end user’s knowledge. It invades the device, steals sensitive information and internet usage data, and relays it to advertisers, data firms or external users.
What is trap phishing?
The phishing messages attempt to lure people to a bogus Web site, where they’re asked to divulge sensitive personal information. The attackers can then use those details to steal money from the victims’ accounts.
What are the attacks on web application?
A Web application attack is any attempt by a malicious actor to compromise the security of a Web-based application. Web application attacks may target either the application itself to gain access to sensitive data, or they may use the application as a staging post to launch attacks against users of the application.
What are the important attacks on web server?
- DOS attack: …
- Website Defacement: …
- Directory Traversal: …
- Misconfiguration attacks: …
- Phishing Attack: …
- Information Gathering: …
- Vulnerability Scanning: …
- Password Attacks:
What is the main purpose of cyber warfare?
According to the Cybersecurity and Infrastructure Security Agency, the goal of cyberwarfare is to “weaken, disrupt or destroy” another nation.
What are the three elements of cybersecurity?
When we discuss data and information, we must consider the CIA triad. The CIA triad refers to an information security model made up of the three main components: confidentiality, integrity and availability. Each component represents a fundamental objective of information security.
What is SEO poisoning?
In search engine optimization (SEO) poisoning attacks, adversaries first compromise legitimate websites and then inject specific keywords into the website that users might commonly search for via their preferred search engine. … Websites hosting the malicious PDF were scattered around the world.
What are Layer 2 attacks?
- Overview. …
- Spanning Tree Protocol (STP) Attacks. …
- Address Resolution Protocol (ARP) Attacks. …
- Media Access Control (MAC) Spoofing. …
- Content Addressable Memory (CAM) Table Overflows. …
- Cisco Discovery Protocol (CDP)/Link Layer Discovery Protocol (LLDP) Reconnaissance. …
- Virtual LAN (VLAN) Hopping.
What is off path attacker?
Unlike a MitM attacker, an off-path attacker cannot observe or modify legitimate packets sent between other parties, however, he can transmit packets with a spoofed (fake) source IP address – impersonating some legitimate party, as illustrated by Off-Path Oscar in Figure 1.
How do you mask an ISP?
- Use a VPN. A VPN is an intermediary server that encrypts your connection to the internet — and it also hides your IP address. …
- Use Tor. Comprising thousands of volunteer-run server nodes, Tor is a free network that conceals your identity online via multiple layers of encryption. …
- Use a proxy.
What are hybrid attacks *?
Hybrid Attacks are a kind of cyberattack where the perpetrator blends two or more kinds of tools to carry out the assault. A typical hybrid attack is one that merges a dictionary attack and a brute-force attack. The former would contain a list of potentially known credential matches (wordlist).
Why would hackers want to cover their tracks?
Explanation: Hackers cover their tracks to keep from having their identity or location discovered.