What is a privilege audit

Mia Kelly
Published Mar 03, 2026
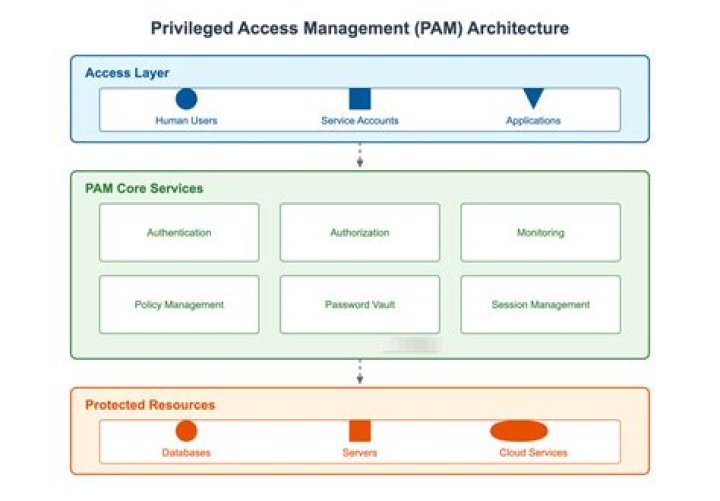
Privilege auditing is the selective auditing of the statements allowed using a system privilege. For example, auditing of the SELECT ANY TABLE system privilege audits users’ statements that are executed using the SELECT ANY TABLE system privilege. You can audit the use of any system privilege.
What is privilege use?
A privileged account is considered to be any account that provides access and privileges beyond those of non-privileged accounts. A privileged user is any user currently leveraging privileged access, such as through a privileged account. … Superusers may even grant and revoke any permissions for other users.
How do you privilege an audit function?
- Access for the privileged user. A privileged user is someone who has access to critical systems and data. …
- Identify and manage privileged access. …
- Monitor privileged user usage. …
- Analyze Behavior. …
- Provide Reports. …
- The Imperva Solution.
What is audit sensitive privilege use?
Audit Sensitive Privilege Use contains events that show the usage of sensitive privileges. This is the list of sensitive privileges: Act as part of the operating system. Back up files and directories.What is usage auditing?
Usage auditing: Usage auditing verifies that systems and software are used appropriately and consistently with organizational policies. A usage audit may include physically inspecting systems and software, and conducting other verification tests as per the polic.
What are privileged users?
Privileged User Accounts are named credentials that have been granted administrative privileges on one or more systems. … Service Accounts can be privileged local or domain accounts that are used by an application or service to interact with the operating system.
What is escalation auditing?
The Audit Committee reserve the right to request attendance and explanation from management where agreed actions resulting from Internal Audit Review’s fall overdue or are not implemented satisfactorily.
What is privileged process?
A privileged process is. [a] computer process that is authorized (and, therefore, trusted) to perform security-relevant functions that ordinary processes are not authorized to perform.What makes a privileged user?
Privileged User Accounts They are the most common form and usually have unique and complex passwords giving them power across the network. These are the accounts that need to be monitored closely. Sometimes, these accounts don’t belong to individual users and are instead shared among admins.
How do you ensure audit sensitive privilege use is set to success and failure?- Open Local Group Policy Editor.
- In the navigation pane, select Computer Configuration > Windows Settings > Security Settings > Advanced Audit Policy Configuration > System Audit Policies – Local Group Policy Object > Privilege Use.
What is audit sensitive?
Audit sensitive means activities of an individual which are normally an element of or subject to significant internal accounting controls.
What is global object access auditing?
Global auditing lets you create System Access Control Lists (SACL) for the entire computer , based on file and registry. This means that instead of manually altering and maintaining SACLs on 10TB of shared files, you can instead define them implicitly and not actually modify the files at all .
How do I track privileged users activities in Active Directory?
Click Start > Administrative Tools > Event Viewer. Expand Windows Logs and select Security. The event viewer now shows all the events recorded in the security logs.
How do you audit access control?
- Create a Security Policy. …
- Develop Formal Procedures. …
- User Review. …
- Assign Appropriate User Privileges. …
- Segregation of Duties. …
- Manage Generic User Accounts. …
- Disable Unnecessary User Accounts. …
- Maintain Clear Documentation.
What is Audit account management?
Audit User Account Management determines whether the operating system generates audit events when specific user account management tasks are performed.
What is permission auditing and review?
An audit that analyzes user privileges. It identifies the privileges (rights and permissions) granted to users, and compares them against what the users need.
How do I enable file system auditing?
- Navigate Windows Explorer to the file you want to monitor.
- Right-click on the target folder/file, and select Properties.
- Security → Advanced.
- Select the Auditing tab.
- Click Add.
- Select the Principal you want to give audit permissions to.
- In the Auditing Entry dialog box, select the types of access you want to audit.
Where are permissions set for viewing audit logs?
Go to Computer Configuration → Policies → Windows Settings → Security Settings. Go to Local Policies → Audit Policy: Audit object access. Select both Success and Failures.
What is meant by privilege escalation?
Privilege escalation can be defined as an attack that involves gaining illicit access of elevated rights, or privileges, beyond what is intended or entitled for a user.
What causes privilege escalation?
Privilege escalation happens when a malicious user exploits a bug, design flaw, or configuration error in an application or operating system to gain elevated access to resources that should normally be unavailable to them.
What is privilege escalation cyber ops?
Privilege escalation is the act of exploiting a bug, a design flaw, or a configuration oversight in an operating system or software application to gain elevated access to resources that are normally protected from an application or user.
What is privilege account?
A privileged account is a user account that has more privileges than ordinary users. … There are many kinds of privileged accounts: Root and administrator accounts are typically used for installing and removing software and changing configuration. They are superuser accounts.
What is privilege level?
Privilege levels define what commands users can enter after they have logged into a network device. This table shows the default password and privilege level configuration.
What are privileged commands?
Definition(s): A human-initiated command executed on an information system involving the control, monitoring, or administration of the system including security functions and associated security-relevant information.
How do I know if a user is privileged?
- Open “Active Directory Users & Computers” on the Domain Controller.
- Select “Built-in” container, right-click on any of the above groups in the right pane, and open its “Properties” windows.
- Go to the “Members” tab; there you will see all members of this group.
What are the consequences of user privilege misuse?
Consequences of privilege abuse Privileged accounts are a gateway to critical systems and data. Abuse of these powerful accounts can lead to the loss of sensitive data and business intelligence, as well as downtime of systems and applications essential for business operations.
How do you protect privileged accounts?
- 1) Track and consolidate each privileged account with an automated discovery mechanism. …
- 2) Store privileged accounts in a secure, centralised vault. …
- 3) Establish clearer roles with limited access privileges.
What is the Chrome sandbox?
The Google Chrome Sandbox is a development and test environment for developers working on Google Chrome browser-based applications. The sandbox environment provides a testing and staging platform without allowing the code being tested to make changes to existing code and databases.
What does sandbox process mean?
This isolates apps from each other and protects apps and the system from malicious apps. To do this, Android assigns a unique user ID (UID) to each Android application and runs it in its own process. … The sandbox is simple, auditable, and based on decades-old UNIX-style user separation of processes and file permissions.
Is sandboxie safe to use?
You would be quite safe using Sandboxie. It should be noted that, from time to time, people are able to find some vulnerability in Sandboxie, an open hole through which malicious software can still infiltrate the system. This is extremely rare and is quickly resolved by closing the hole that is the attack vector.
How do I configure advanced audit policy?
Under Computer Configuration, click Policies > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Audit Policy, then double-click on the relevant policy setting. In the right pane, right-click on the relevant Subcategory, and then click Properties.