What can AWS Macie detect

William Taylor
Published Feb 17, 2026
Macie automatically detects a large and growing list of sensitive data types, including personally identifiable information (PII) such as names, addresses, and credit card numbers. It also gives you constant visibility of the data security and data privacy of your data stored in Amazon S3.
Is AWS Macie only for S3?
As you use Macie to monitor and assess the security posture of your Amazon S3 data, keep the following in mind: Inventory data applies only to S3 buckets in the current AWS Region. To access the data for additional Regions, enable and use Macie in each additional Region.
Which of the following is the feature of Amazon Macie?
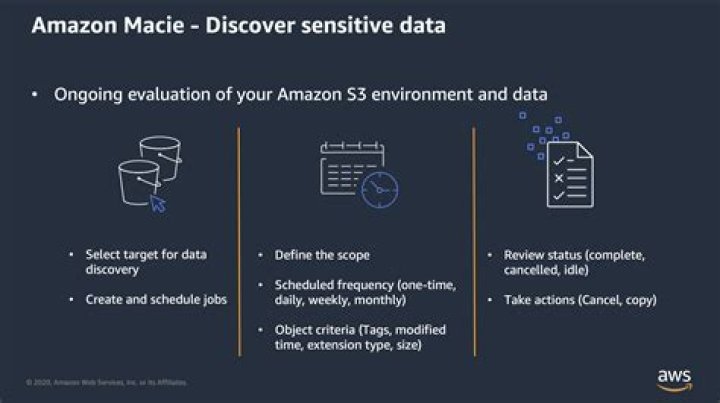
Amazon Macie allows you to run one-time, daily, weekly, or monthly sensitive data discovery jobs for all, or a subset of objects in an Amazon S3 bucket. For sensitive data discovery jobs, Amazon Macie automatically tracks changes to the bucket and only evaluates new or modified objects over time.
Why is it called AWS Macie?
The first meaning of Macie that was found, said that that name meant “weapon”. The second meaning noted the name was representative of a person that is bold, sporty, and sweet.How do you use Macie?
- Before you begin.
- Step 1: Enable Amazon Macie.
- Step 2: Configure a repository for sensitive data discovery results.
- Step 3: Explore sample findings.
- Step 4: Create a job to discover sensitive data.
- Step 5: Review your findings.
What is Snowball AWS?
Description: Snowball is a petabyte-scale data transport solution that uses secure appliances to transfer large amounts of data into and out of the AWS cloud. Using Snowball addresses common challenges with large-scale data transfers including high network costs, long transfer times, and security concerns.
What are some examples of suspicious activity that Amazon Macie can detect?
- An account that downloads large amounts of sensitive data;
- Unusual activity from an unfamiliar IP address;
- A user who downloads source code that he or she doesn’t normally interact with it; and.
- Sensitive data being granted global access inadvertently.
What does AWS inspector do?
AWS Inspector is a Security vulnerability tool used to assess the network visibility and security vulnerability posture of your EC2 instances. … AWS inspector is capable of both network and host level assessments.What is AWS xray?
AWS X-Ray is a service that helps developers analyze and debug distributed applications. Customers use X-Ray to monitor application traces, including the performance of calls to other downstream components or services, in either cloud-hosted applications or from their own machines during development.
What is code star in AWS?AWS CodeStar is a cloud‑based development service that provides the tools you need to quickly develop, build, and deploy applications on AWS. With AWS CodeStar, you can set up your entire continuous delivery toolchain in minutes, allowing you to start releasing code faster.
Article first time published onWhat does Macie scan for?
Macie automatically detects a large and growing list of sensitive data types, including personal identifiable information (PII) such as names, addresses, and credit card numbers.
What is AWS firewall manager?
AWS Firewall Manager is a security management service which allows you to centrally configure and manage firewall rules across your accounts and applications in AWS Organizations. … You can deploy AWS Network Firewalls across accounts and VPCs in your organization.
What does CloudTrail capture?
Actions taken by a user, role, or an AWS service are recorded as events in CloudTrail. Events include actions taken in the AWS Management Console, AWS Command Line Interface, and AWS SDKs and APIs. … When activity occurs in your AWS account, that activity is recorded in a CloudTrail event.
What is Athena query?
Amazon Athena is an interactive query service that makes it easy to analyze data in Amazon S3 using standard SQL. Athena is serverless, so there is no infrastructure to manage, and you pay only for the queries that you run. … This makes it easy for anyone with SQL skills to quickly analyze large-scale datasets.
Which service would be used to send alerts based on Amazon CloudWatch alarms?
Using Amazon CloudWatch alarms, you can set up metric thresholds and send alerts to Amazon Simple Notification Service (SNS).
How do you use AWS Kendra?
- Create an AWS Account. …
- Set up the Amazon Kendra index. …
- Update the IAM role. …
- Configure an S3 connector to the data source. …
- Add an FAQ. …
- Query the index. …
- Clean up.
What is AWS edge?
AWS edge services deliver data processing, analysis, and storage close to your endpoints, allowing you to deploy APIs and tools to locations outside AWS data centers. … With 200+ integrated device services to choose from, you can deploy edge applications quickly and easily scale to billions of devices.
What can AWS Lambda do?
AWS Lambda is a serverless compute service that runs your code in response to events and automatically manages the underlying compute resources for you. … You can use AWS Lambda to extend other AWS services with custom logic, or create your own backend services that operate at AWS scale, performance, and security.
Is EC2 a compute service?
Amazon EC2. Amazon Elastic Compute Cloud (Amazon EC2) is a web service that provides secure, resizable compute capacity in the cloud. It is designed to make web-scale computing easier for developers. The simple web interface of Amazon EC2 allows you to obtain and configure capacity with minimal friction.
What is CodeDeploy AWS?
AWS CodeDeploy is a fully managed deployment service that automates software deployments to a variety of compute services such as Amazon EC2, AWS Fargate, AWS Lambda, and your on-premises servers. … You can use AWS CodeDeploy to automate software deployments, eliminating the need for error-prone manual operations.
What is AWS code guru?
Amazon CodeGuru is a developer tool that provides intelligent recommendations to improve your code quality and identify an application’s most expensive lines of code.
What is AWS CloudTrail?
AWS CloudTrail enables auditing, security monitoring, and operational troubleshooting by tracking user activity and API usage. CloudTrail logs, continuously monitors, and retains account activity related to actions across your AWS infrastructure, giving you control over storage, analysis, and remediation actions.
What is CloudWatch AWS?
Amazon CloudWatch is a monitoring and management service that provides data and actionable insights for AWS, hybrid, and on-premises applications and infrastructure resources. … You can use CloudWatch Container Insights to monitor, troubleshoot, and alert your containerized applications and microservices.
What is AWS inspector VS trusted advisor?
AWS Inspector leverages agents installed on EC2 instances and performs assessments against templates and reports results and violations. AWS Advisor, on the other hand, works at a higher level and provide guidance to provision resources following AWS best practices.
What is AWS access analyzer?
AWS IAM Access Analyzer helps you identify the resources in your organization and accounts, such as Amazon S3 buckets or IAM roles, shared with an external entity. This lets you identify unintended access to your resources and data, which is a security risk.
What is Cloud9 server?
AWS Cloud9 is a cloud-based integrated development environment (IDE) that lets you write, run, and debug your code with just a browser. … With Cloud9, you can quickly share your development environment with your team, enabling you to pair program and track each other’s inputs in real time.
What is AWS in DevOps?
AWS provides services that help you practice DevOps at your company and that are built first for use with AWS. These tools automate manual tasks, help teams manage complex environments at scale, and keep engineers in control of the high velocity that is enabled by DevOps.
What is meant by CodeStar?
AWS CodeStar is a cloud-based service for creating, managing, and working with software development projects on AWS. You can quickly develop, build, and deploy applications on AWS with an AWS CodeStar project. … AWS CodeStar also manages the permissions required for project users (called team members).
What are snowball edge versions?
Snowball Edge devices have three options for device configurations—Storage Optimized, Compute Optimized, and Compute Optimized with GPU. When this guide refers to Snowball Edge devices, it’s referring to all options of the device.
Has AWS ever been hacked?
The most recent data breach involving Amazon itself occurred in October 2020, when a disgruntled Amazon employee leaked customer data to a third party for the second time that year. There have also been numerous breaches in Amazon Web Services (AWS) over the years, most often due to improperly configured S3 buckets.
Why does Amazon need a firewall?
Why does Amazon need a firewall? Amazon needs firewall because it provides a barrier which prevents unauthorized access. Firewall also enhances security of devices connected to the internet. Firewall also helps amazon to monitor traffic and block the unwanted traffic.