How does TLS protocol work

Rachel Hickman
Published Apr 02, 2026
TLS is an encryption protocol designed to secure Internet communications. … During a TLS handshake, the two communicating sides exchange messages to acknowledge each other, verify each other, establish the encryption algorithms they will use, and agree on session keys.
How the TLS protocol works?
TLS is an encryption protocol designed to secure Internet communications. … During a TLS handshake, the two communicating sides exchange messages to acknowledge each other, verify each other, establish the encryption algorithms they will use, and agree on session keys.
How does TLS and SSL work?
How does SSL/TLS work? … Secure communication begins with a TLS handshake, in which the two communicating parties open a secure connection and exchange the public key. During the TLS handshake, the two parties generate session keys, and the session keys encrypt and decrypt all communications after the TLS handshake.
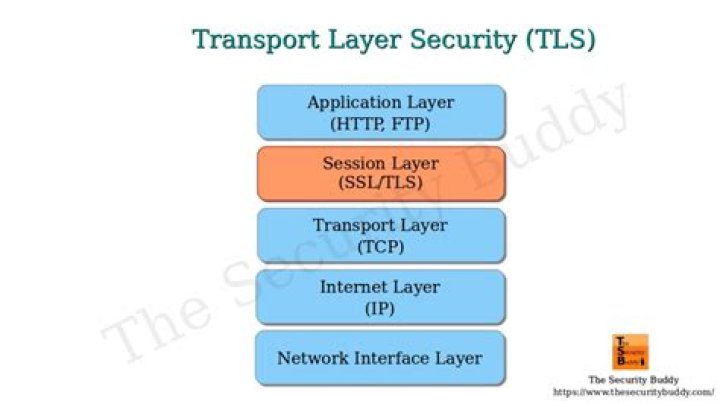
What protocol does TLS use?
TLS is normally implemented on top of TCP in order to encrypt Application Layer protocols such as HTTP, FTP, SMTP and IMAP, although it can also be implemented on UDP, DCCP and SCTP as well (e.g. for VPN and SIP-based application uses).How TLS connection is established?
How is a TLS connection established? In a TLS connection, the client and the server first agree upon the version of TLS that they are going to use, which is the highest that both support. Then, they agree upon cipher suites that they are going to use.
Does TLS encrypt TCP header?
The TCP header and payload are encrypted by TLS. Because encryption is performed in the protocol on one end system and decryption in the protocol of the other end system, the packet payload remains encrypted along the entire path.
Does TLS use AES?
TLS uses many encryption algorithms, including AES in various modes, and several hash algorithms, including those in the SHA family. TLS may also use encryption algorithms not based on a block cipher, such as RC4.
Why is TLS needed?
Transport Layer Security (TLS) is a crucial part of cybersecurity protocols for organizations of any size, including managed services providers (MSPs). TLS is designed to secure data against hackers and helps ensure that sensitive information such as passwords and credit card numbers are safe.What are the two protocols that TLS uses?
It runs in the application layer and is itself composed of two layers: the TLS record and the TLS handshake protocols.
What are the 3 main security purposes of TLS?There are three main components to what the TLS protocol accomplishes: Encryption, Authentication, and Integrity. Encryption: hides the data being transferred from third parties. Authentication: ensures that the parties exchanging information are who they claim to be.
Article first time published onHow does TLS certificate verification work?
How does a TLS certificate work? When a user tries to connect to a server, the server sends them its TLS certificate. The user then verifies the server’s certificate using CA certificates that are present on the user’s device to establish a secure connection.
How do I enable TLS?
- Open Google Chrome.
- Click Alt F and select Settings.
- Scroll down and select Show advanced settings…
- Scroll down to the Network section and click on Change proxy settings…
- Select the Advanced tab.
- Scroll down to Security category, manually check the option boxes for Use TLS 1.0,Use TLS 1.1 and Use TLS 1.2.
Is TLS asymmetric?
SSL/TLS uses both asymmetric and symmetric encryption to protect the confidentiality and integrity of data-in-transit. Asymmetric encryption is used to establish a secure session between a client and a server, and symmetric encryption is used to exchange data within the secured session.
How do you connect over TLS?
- Open the TCP/UDP Path Options dialog box for the path used for the connection.
- Set Security type to the version you require.
- Click PKI Settings to open the PKI Settings dialog box.
How do I know if I have TLS packets?
- Observe the traffic captured in the top Wireshark packet list pane.
- Select the third TLS packet, labeled Certificate, Server Key Exchange, Server Hello Done.
- Observe the packet details in the middle Wireshark packet details pane.
How does TLS authentication?
How SSL and TLS provide confidentiality. SSL and TLS use a combination of symmetric and asymmetric encryption to ensure message privacy. During the SSL or TLS handshake, the SSL or TLS client and server agree an encryption algorithm and a shared secret key to be used for one session only.
Does TLS encrypt the payload?
TLS uses symmetric-key encryption to provide confidentiality to the data that it transmits. Unlike public-key encryption, just one key is used in both the encryption and decryption processes. Once data has been encrypted with an algorithm, it will appear as a jumble of ciphertext.
Does TLS use SHA256?
Yes, you can buy a SHA256 certificate for TLS 1.0, TLS 1.1 and TLS 1.2 communication. However, using SHA256 certificate as SSL certificate, clients must support SHA256 hash algorithm to be able to validate the SSL certificate.
How does TLS work with TCP?
TLS encrypts data before it reaches TCP (or other transports), and decrypts it after being handed over by the transport at the other end. It also handles the necessary key exchange. TCP is a socket channel over the internet and TLS is encrypted channel on top of TCP.
Does TLS use TCP or UDP?
TLS was designed to operate on top of a reliable transport protocol such as TCP. However, it has also been adapted to run over datagram protocols such as UDP.
Does TLS work with UDP?
TLS cannot go directly on top of UDP. This is because, in UDP, packets might be lost or get out of order and TLS does not have the tools to address these problems: … TLS uses implicit sequence numbers while the DTLS protocol uses explicit sequence numbers to resolve this problem.
Why is TLS 1.0 insecure?
TLS 1.0 has several flaws. An attacker can cause connection failures and they can trigger the use of TLS 1.0 to exploit vulnerabilities like BEAST (Browser Exploit Against SSL/TLS). Websites using TLS 1.0 are considered non-compliant by PCI since 30 June 2018.
What is difference between TLS and SSL?
Transport Layer Security (TLS) is the successor protocol to SSL. TLS is an improved version of SSL. It works in much the same way as the SSL, using encryption to protect the transfer of data and information. The two terms are often used interchangeably in the industry although SSL is still widely used.
How does a TCP connection work?
TCP organizes data so that it can be transmitted between a server and a client. It guarantees the integrity of the data being communicated over a network. Before it transmits data, TCP establishes a connection between a source and its destination, which it ensures remains live until communication begins.
How much does TLS cost?
This type of certificate may take a few days for processing, but it’s highly recommended for e-commerce platforms and sites that deal in sensitive information. They are the most expensive SSL certificate, and they generally cost over $100 per year.
How does a CERT work?
The certificate is signed by the Issuing Certificate authority, and this it what guarantees the keys. Now when someone wants your public keys, you send them the certificate, they verify the signature on the certificate, and if it verifies, then they can trust your keys.
Does TLS encrypt email attachments?
There are a few different ways to encrypt emails, starting from the broad network-level protection called TLS (transport layer security). … However, TLS doesn’t provide complete security: emails outside the server or individual attachments aren’t protected. The next level of protection is end-to-end encryption.
Does TLS encrypt data in transit?
For example, Transport Layer Security (TLS) is often used to encrypt data in transit for transport security, and Secure/Multipurpose Internet Mail Extensions (S/MIME) is used often for email message security.
Why is OpenSSL needed?
Why do you need OpenSSL? With OpenSSL, you can apply for your digital certificate (Generate the Certificate Signing Request) and install the SSL files on your server. You can also convert your certificate into various SSL formats, as well as do all kind of verifications.
Is TLS 1.2 Vulnerable?
Bad news: there’s a vulnerability in TLS 1.2. Good news: researchers say it’s “very hard to exploit” and major vendors have already released security patches for it.
How do I renew my TLS certificate?
- Step 1: Generate CSR. To renew an SSL/TLS certificate, you’ll need to generate a new CSR. …
- Step 2: Sign in to your account. Sign in to your CertCentral account.
- Step 3: Fill out the renewal form. …
- Step 4: DigiCert issues the SSL/TLS certificate. …
- Step 5: Install your renewed SSL/TLS certificate.