How do I get my CSRF token

Christopher Lucas
Published Apr 06, 2026
1) In Chrome/Firefox, open the console by right clicking anywhere and chose “inspect”(for Chrome) or “inspect element”(for Firefox). Do a get request or login first while you see the request made , to get CSRF-TOKEN sent from the server. 5) In the next post request, use the CSRF-TOKEN from the previous request.
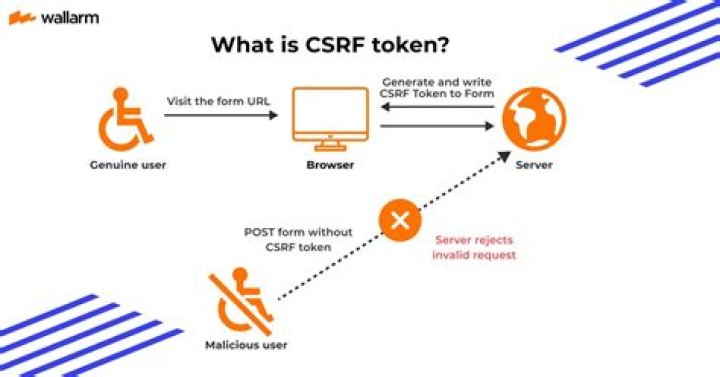
What is CSRF What is the purpose of the CSRF token?
A CSRF Token is a secret, unique and unpredictable value a server-side application generates in order to protect CSRF vulnerable resources. The tokens are generated and submitted by the server-side application in a subsequent HTTP request made by the client.
How do I fix CSRF verification failed aborted?
- Disable autofill, allow cookies, and clear your cache.
- Reset your password using Chrome.
Do I need CSRF token?
CSRF tokens prevent CSRF because without token, attacker cannot create a valid requests to the backend server. CSRF tokens should not be transmitted using cookies. The CSRF token can be added through hidden fields, headers, and can be used with forms, and AJAX calls.What is Csurf?
We are Colorado State University Research Foundation. However, we are more than our name suggests. We advance CSU led research and innovation. We provide resources for the enrichment of the Colorado State University System and community. This is CSURF.
How do tokens prevent CSRF?
CSRF tokens can prevent CSRF attacks by making it impossible for an attacker to construct a fully valid HTTP request suitable for feeding to a victim user.
Does JWT prevent CSRF?
If you put your JWTs in a header, you don’t need to worry about CSRF. You do need to worry about XSS, however. If someone can abuse XSS to steal your JWT, this person is able to impersonate you.
Does Authorization header prevent CSRF?
This is a type of HTTP authentication where the user is identified through a token that is submitted in “Authorization” header of each request. This mechanism solves CSRF because unlike cookies it is not submitted by the browser automatically.What is XSS and CSRF?
Cross-site scripting (or XSS) allows an attacker to execute arbitrary JavaScript within the browser of a victim user. Cross-site request forgery (or CSRF) allows an attacker to induce a victim user to perform actions that they do not intend to.
Is CSRF token a cookie?The CSRF token in fact could be the standard authentication cookie when using this method, and this value is submitted via cookies as usual with the request, but the value is also repeated in either a hidden field or header, of which an attacker cannot replicate as they cannot read the value in the first place.
Article first time published onHow does CSRF work in Spring Security?
CSRF (Cross Site Request Forgery) is a technique in which an attacker attempts to trick you into performing an action using an existing session of a different website. Spring Security when combined with Thymeleaf templates, automatically inserts a token into all web forms as a hidden field.
What does this mean CSRF verification failed request aborted?
CSRF verification failed. Request aborted. You are seeing this message because this site requires a CSRF cookie when submitting forms. This cookie is required for security reasons, to ensure that your browser is not being hijacked by third parties.
What is CSRF token missing or incorrect?
Invalid or missing CSRF token This error message means that your browser couldn’t create a secure cookie, or couldn’t access that cookie to authorize your login. This can be caused by ad- or script-blocking plugins, but also by the browser itself if it’s not allowed to set cookies.
How do I enable CSRF cookies in Safari?
Open Safari Preferences from the drop-down menu in the navigation bar or by typing Cmd + , (⌘,). Click the Privacy tab and make sure that “Cookies and website data” is set to either “Always allow” or “Allow from websites I visit”.
How does Csurf work?
The csurf works by storing a token secret into either the session (in the case of express-session ) or directly into cookie (case of cookie-parser ). The server side should then render the website with a dynamically generated (per request) token via req. csrfToken() .
What is Csurf in node?
Node. js CSRF protection middleware. Requires either a session middleware or cookie-parser to be initialized first. express-session. …
What is Csurf in node JS?
Csurf module in Node. js prevents the Cross-Site Request Forgery(CSRF) attack on an application. By using this module, when a browser renders up a page from the server, it sends a randomly generated string as a CSRF token.
Is JWT secure enough?
The contents in a json web token (JWT) are not inherently secure, but there is a built-in feature for verifying token authenticity. A JWT is three hashes separated by periods. The third is the signature.
What is difference between JWT and CSRF token?
An authentication system based on tokens (JWT or random) stored in cookies is vulnerable to CSRF attacks, because cookies are sent automatically to server in each request and an attacker could build a harmful url link to your site.
How long should a JWT last?
The JWT access token is only valid for a finite period of time. Using an expired JWT will cause operations to fail. As you saw above, we are told how long a token is valid through expires_in. This value is normally 1200 seconds or 20 minutes.
What's the most effective measure to take against a CSRF?
The most popular method to prevent Cross-site Request Forgery is to use a challenge token that is associated with a particular user and that is sent as a hidden value in every state-changing form in the web app.
Can CSRF token be stolen?
Stealing Anti-CSRF Tokens: When CSRF tokens are passed as cookie parameters without Secure and HTTPOnly flags, an attacker can potentially steal the CSRF token via XSS or other attacks.
What is XSRF protection?
Cross-site request forgery (also known as XSRF or CSRF) is an attack against web-hosted apps whereby a malicious web app can influence the interaction between a client browser and a web app that trusts that browser.
Does HTML encoding prevent XSS?
No. Putting aside the subject of allowing some tags (not really the point of the question), HtmlEncode simply does NOT cover all XSS attacks.
Is CSRF a vulnerability?
Cross-site request forgery (also known as CSRF) is a web security vulnerability that allows an attacker to induce users to perform actions that they do not intend to perform.
What is the difference between XSS and SQL injection?
What is the difference between XSS and SQL injection? XSS is a client-side vulnerability that targets other application users, while SQL injection is a server-side vulnerability that targets the application’s database.
Which of the following are the most common results of a cross site request forgery?
It can result in damaged client relationships, unauthorized fund transfers, changed passwords and data theft—including stolen session cookies. CSRFs are typically conducted using malicious social engineering, such as an email or link that tricks the victim into sending a forged request to a server.
How can cross site request forgery CSRF be prevented?
Validating Requests. Attackers can perform a CSRF attack if they know the parameters and values to send in a form or in a query string. To prevent those attacks, you need a way to distinguish data sent by the legitimate user from the one sent by the attacker.
Is it good to store CSRF token in cookie?
Your web application generates CSRF token values inside cookies which is not a best practice for web applications as revelation of cookies can reveal CSRF Tokens as well. Authenticity tokens should be kept separate from cookies and should be isolated to change operations in the account only.
What is Django Csrf_token?
The CSRF token is like an alphanumeric code or random secret value that’s peculiar to that particular site. Hence, no other site has the same code. In Django, the token is set by CsrfViewMiddleware in the settings.py file. A hidden form field with a csrfmiddlewaretoken field is present in all outgoing requests.
What is double submit cookie?
Double submitting cookies is defined as sending a random value in both a cookie and as a request parameter, with the server verifying if the cookie value and request value are equal.