Does S3 support encryption

Sophia Edwards
Published Apr 27, 2026
Within Amazon S3, Server Side Encryption (SSE) is the simplest data encryption option available. SSE encryption manages the heavy lifting of encryption on the AWS side, and falls into two types: SSE-S3 and SSE-C.
How do I encrypt data before sending to S3?
Use the AES key to encrypt data on the client side before sending it to Amazon S3. Use the AES key to decrypt data received from Amazon S3.
Does AWS encrypt data?
All AWS services that handle customer data encrypt data in motion and provide options to encrypt data at rest. All AWS services that offer encryption at rest using AWS KMS or AWS CloudHSM use AES-256.
What does S3 encryption protect against?
Disk encryption protects you against data loss when a disk is stolen and the key is not stolen with it. Such examples might be, as Gilles says, stolen backups, but could also be in laptops on the move, or disposed of hard disks to prevent meaningful attempts at salvaging data from your decommissioned disks.How do I encrypt an object on my Galaxy S3?
- Sign into the AWS Management Console.
- Navigate to the S3 console and find the bucket and object that was flagged as unencrypted.
- Select the object and choose Properties then Encryption.
- Use the wizard to choose the S3 encryption options you prefer.
- Save to apply encryption to the object.
Which methods are available to encrypt data in S3?
- Amazon S3-managed Encryption Keys (SSE-S3) In this scenario the keys are managed by S3 itself and are only usable for S3 services.
- KMS-managed Encryption Keys (SSE-KMS) …
- Customer-provided Encryption Keys (SSE-C)
Does S3 encryption cost?
$1.001 KMS key$5.971,990,000 requests (2,010,000 total requests – 20,000 free tier requests) x $0.03 / 10,000 requests$2,380.8031 days for 2 HSMs x $1.60 / HSM / hourTotal:$2,387.77/month
What is SSE S3 encryption?
SSE-S3 is the simplest method to use as encryption keys are handled and managed by AWS. SSE-S3 is based on AES-256 encryption algorithm, a symetric cypher. You cannot access this key or use it manually for any other encryption processing. The key is itself encrypted with a master key that is regularly rotated.How do I protect data on my Galaxy S3?
- Implement server-side encryption.
- Enforce encryption of data in transit.
- Consider using Macie with Amazon S3.
- Identify and audit all your Amazon S3 buckets.
- Monitor Amazon Web Services security advisories.
There are no additional charges for using default encryption for S3 buckets. Requests to configure the default encryption feature incur standard Amazon S3 request charges.
Article first time published onDo AWS key pairs cost?
You only pay US $1/month to store any key that you create. AWS managed keys that are created on your behalf by AWS services are free to store. You are charged per-request when you use or manage your keys beyond the free tier.
What is the difference between SSE S3 and SSE kms?
SSE-KMS is similar to SSE-S3 but comes with some additional benefits over SSE-S3. Unlike SSE-S3 you can create and manage encryption keys yourself or you can use a default CMK key that is unique to you for the service that is being used (S3 in this case) and the region you are working in.
Can AWS decrypt data?
AWS services encrypt your data and store an encrypted copy of the data key along with the encrypted data. When a service needs to decrypt your data, it requests AWS KMS to decrypt the data key using your KMS key.
What is cloud kms?
Google Cloud Key Management Service (KMS) is a cloud service for managing encryption keys for other Google cloud services that enterprises can use to implement cryptographic functions. … Administrators can also use Google Cloud KMS to do bulk data encryption on plaintext before it is stored.
How secure is KMS?
Secure: In AWS KMS, keys are generated and protected in Hardware security modules (HSMs) validated under FIPS 140-2. For security, keys are only used inside HSMs and can never be shared outside the AWS region in which they were created.
Is security group free AWS?
There is no charge applicable to Security Groups in Amazon EC2 / Amazon VPC. You can drill-down into your billing charges via the Billing Dashboard. Just click Bill Details, expand the Elastic Compute Cloud section and a breakdown of charges will be displayed.
How does S3 default encryption work?
Ensure that default encryption is enabled at the bucket level to automatically encrypt all objects when stored in Amazon S3. The S3 objects are encrypted during the upload process using Server-Side Encryption with either AWS S3-managed keys (SSE-S3) or AWS KMS-managed keys (SSE-KMS).
What is Amazon S3 encryption client?
The Amazon S3 Encryption Client is a convenient and efficient tool for performing client-side encryption of objects in S3. … Amazon S3 supports three options for server-side encryption. One option is for S3 to fully manage the encryption keys (SSE-S3).
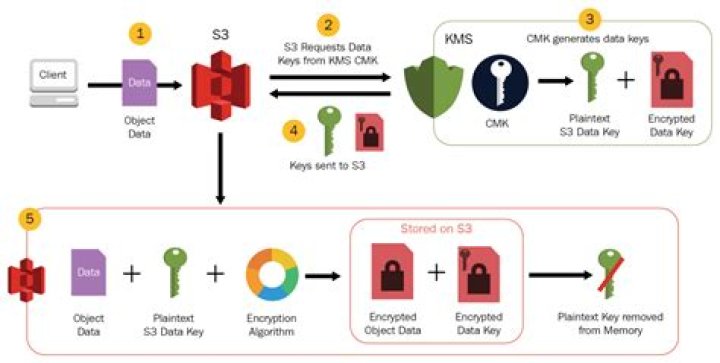
What is AWS kms S3?
AWS Key Management Service (AWS KMS) is a service that combines secure, highly available hardware and software to provide a key management system scaled for the cloud. Amazon S3 uses AWS KMS keys to encrypt your Amazon S3 objects. AWS KMS encrypts only the object data. Any object metadata is not encrypted.
What action does the S3 master key perform in the SSE S3 encryption and decryption process?
Amazon S3 sends the encrypted data key to AWS KMS. AWS KMS decrypts the key by using the same KMS key and returns the plaintext data key to Amazon S3. Amazon S3 decrypts the ciphertext and removes the plaintext data key from memory as soon as possible.
What is a CMK?
A Customer Master Key (CMK) is a Key Encryption Key (KEK) created by a user on KMS. It is used to encrypt and protect DEKs. One CMK can be used to encrypt one or more DEKs. CMKs are categorized into custom keys and default keys. Custom keys.
How do I encrypt and decrypt AWS?
To decrypt an encrypted data key, and then immediately re-encrypt the data key under a different AWS KMS key, use the ReEncrypt operation. The operations are performed entirely on the server side within AWS KMS, so they never expose your plaintext outside of AWS KMS.