Are JSON Web Tokens secure

Sophia Edwards
Published Mar 04, 2026
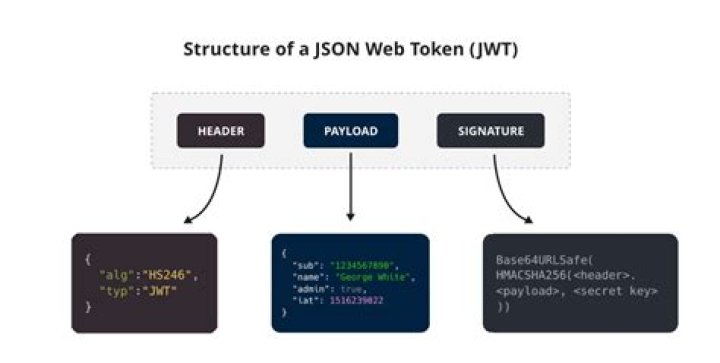
The general opinion is that they’re good for being used as ID Tokens or Access Tokens and that they’re secure – as the tokens are usually signed or even encrypted. … A JSON Web Token (JWT, pronounced “jot”) is a compact and url-safe way of passing a JSON message between two parties. It’s a standard, defined in RFC 7519.
Can JWT token be stolen?
What Happens if Your JSON Web Token is Stolen? In short: it’s bad, real bad. Because JWTs are used to identify the client, if one is stolen or compromised, an attacker has full access to the user’s account in the same way they would if the attacker had instead compromised the user’s username and password.
Can JWT be decoded?
A valid JWT can consist of just the header and payload sections. … By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token’s integrity.
What is so special about JSON Web Tokens?
Information Exchange: JWTs are a good way of securely transmitting information between parties because they can be signed, which means you can be sure that the senders are who they say they are. Additionally, the structure of a JWT allows you to verify that the content hasn’t been tampered with.Is it safe to pass JWT in url?
A JSON Web Token (JWT, pronounced “jot”) is a compact and url-safe way of passing a JSON message between two parties. It’s a standard, defined in RFC 7519.
Where are JSON Web Tokens stored?
A JWT needs to be stored in a safe place inside the user’s browser. If you store it inside localStorage, it’s accessible by any script inside your page. This is as bad as it sounds; an XSS attack could give an external attacker access to the token.
Is JWT better than session?
In modern web applications, JWTs are widely used as it scales better than that of a session-cookie based because tokens are stored on the client-side while the session uses the server memory to store user data, and this might be an issue when a large number of users are accessing the application at once.
Can you decode JWT without secret?
1 Answer. There are two ways in which a public/private keys can be used by a JWT: signing and encryption. If you use a private key for signing, it allows for the recipient to identify the sender of the JWT and the integrity of the message but not to hide its contents from others (confidentiality).Is JWT authentication or authorization?
JSON Web Token (JWT) is an open standard for securely transmitting information between parties as a JSON object. … JWT is commonly used for authorization. JWTs can be signed using a secret or a public/private key pair.
Is JWT the same as OAuth?Basically, JWT is a token format. OAuth is an standardised authorization protocol that can use JWT as a token. OAuth uses server-side and client-side storage. If you want to do real logout you must go with OAuth2.
Article first time published onIs token authentication secure?
Because tokens can only be gleaned from the device that produces them—whether that be a key fob or smartphone—token authorization systems are considered highly secure and effective. But despite the many advantages associated with an authentication token platform, there is always a slim chance of risk that remains.
Is token in URL safe?
If you place a session token directly in the URL, it increases the risk of an attacker capturing and exploiting it. … When you connect to the web server using HTTPS the risk is less than if you use HTTP but it is still a threat. HTTPS URLs are encrypted during transmission but they are often stored in server logs.
What if refresh token is stolen?
If the refresh token can be stolen, then so can the access token. With such an access token, the attacker can start making API calls. To make matters even more complicated, access tokens are often self-contained JWT tokens. Such tokens contain all the information needed for the API to make security decisions.
Is session a cookie?
Sessions use a cookie! Session data is stored on the server side, but a UID is stored on client side in a cookie.
What is more secure JWT or cookies?
1 Answer. There are several reasons people say JWTs are more secure. … JWT can either be stored in a cookie or Web Storage( local/session Storage ). If you are not storing your JWTs in a cookie, then you are not vulnerable to CSRF.
Does Google use JWT or sessions?
Google does not use JWTs for user sessions in the browser. They use regular cookie sessions. JWTs are used purely as Single Sign On transports so that your login session on one server or host can be transferred to a session on another server or host.
Is it safe to store access token in local storage?
Local storage is vulnerable because it’s easily accessible using JavaScript and an attacker can retrieve your access token and use it later. However, while httpOnly cookies are not accessible using JavaScript, this doesn’t mean that by using cookies, you are safe from XSS attacks involving your access token.
Is it safe to store token in cookie?
With cookies, the access token is still hidden, attackers could only carry out “onsite” attacks. The malicious scripts injected into the web app could be limited, or it might not be very easy to change/inject more scripts. Users or web apps might need to be targeted first by attackers.
Is it safe to store access token in cookie?
Is the access_token stored in cookie encrypted or not (it definitely should be) Access_token is a bearer token so it is not tied to browser flows. Cookies in general are meant for maintaining state in browsers. So if lifecycle of token is same as cookie, go ahead otherwise not.
How long should JWT tokens last?
JWT Token has an expiration of 2 hours. The token is refreshed every hour by the client. If the user token is not refreshed (user is inactive and the app is not open) and expires, they will need to log in whenever they want to resume.
How do I authenticate with JWT tokens?
To authenticate a user, a client application must send a JSON Web Token (JWT) in the authorization header of the HTTP request to your backend API. API Gateway validates the token on behalf of your API, so you don’t have to add any code in your API to process the authentication.
How is JWT token validated?
- Verify that the JWT contains three segments, separated by two period (‘. …
- Parse the JWT to extract its three components.
Is JWT a bearer?
RFC 7519: JSON Web Token JSON Web Token (JWT, RFC 7519) is a way to encode claims in a JSON document that is then signed. JWTs can be used as OAuth 2.0 Bearer Tokens to encode all relevant parts of an access token into the access token itself instead of having to store them in a database.
Can JWT be used without OAuth?
Don’t Leave JWT All Alone The simple fact is that JWTs are a great solution, especially when used in tandem with something like OAuth. Those benefits quickly disappear when used alone, and in many cases can result in worse overall security.
What can I use instead of a JWT?
- OAuth2. …
- Passport. …
- Spring Security. …
- Auth0. …
- Amazon Cognito. …
- Keycloak. …
- Firebase Authentication. …
- Devise.
Why we use token based authentication in Web API?
Token-based authentication is a process where the client application first sends a request to Authentication server with a valid credentials. The Authentication server sends an Access token to the client as a response. This token contains enough data to identify a particular user and it has an expiry time.
How do secure tokens work?
Security tokens authenticate identities electronically by storing personal information. They are issued by Security Token Services (STS), which authenticate the person’s identity. They may be used in place of or in addition to a password to prove the owner’s identity.
What is a website security token?
A security token is a physical or digital device that provides two-factor authentication (2FA) for a user to prove their identity in a login process. … They are most commonly used to access computer networks but also can secure physical access to buildings and act as electronic signatures for documents.
What does token mean in URL?
Tokens are generated within your web application and appended to URLs in a query string. Requests are authenticated at Fastly’s edge instead of your origin server. When Fastly receives a request for the URL, the token is validated before serving the content. After a configurable period of time, the token expires.
How can I hide my session ID?
If you have set cookieless to false in your web. config file and it is still showing the sessionid in url, it means the browser has cookies disabled. Check the browser setting and enable the browser to accept cookies. There is no way to hide the sessionid if cookies are disabled for a browser.
What is the difference between session ID and session token?
SO YOU ARE PROBABLY WONDERING WHAT IS THE DIFFERENCE BETWEEN A TOKEN AND A SESSION_ID STORED IN A COOKIE: The difference is that tokens are typically following a standard while sessions are implemented as needed by the server. Additionally, tokens tend not to need a session on the server but they may have one.